The vulnerability of any cryptosystem needs to be subjected to stringent
tests before it can be implemented. In fact the very growth of new and efficient
cryptographic schemes depends a lot on the input of cryptanalysts, who make
a thorough study of possible loopholes and susceptibility to attacks. A study
of possible methods that endanger a system would require a book of its own.
Possible attacks on a cryptosystem are
1. Decoding: the most obvious of all — an eavesdropper intercepts the
message and solves for the decoding keys
2. Eavesdropping (the message is intercepted and decoded) if detected,
means that the channel is insecure and needs protection or needs to be
dropped altogether
3. Man-in-the-middle or impersonation: an eavesdropper having access to
the channel impersonates the sender and thus gets information about
the decoding scheme, or else foils the communication. This is especially
true when there is no means of authenticating the sender
4. Denial of service: the eavesdropper is able to clog the communication
channel or even cut it off physically and prevent the transmission of
messages.
5. Other attacks specific to the hardware and protocols being used.
9.4 Quantum Key Distribution
Quantum key distribution is potentially secure because of the fundamental
properties of the quantum states used. The first schemes of quantum key
distribution relied on the indistinguishability of non-orthogonal states and the
no-cloning principle. Another reason why quantum key distribution has been
such a resounding success is that the protocols are feasible and immediately
implementable using available optical technology. Quanta of light, photons,
are used to carry qubits. The two basis states are implemented by the two
orthogonal states of polarization of the light. Various bases can be used to
represent the polarization. Linearly polarized light in different basis states
Information and Communication 189
can be easily produced by passing light through a polarizer with pass axis
oriented along different directions.
-basis:
|0i : horizontally polarized : |↔i (9.7a)
|1i : vertically polarized : |li. (9.7b)
H-basis:
|+i = H|0i : polarized at + 45
◦
: |
l
i (9.8a)
|−i = H|1i : polarized at − 45
◦
: |
l
i. (9.8b)
The circular polarization basis is also sometimes used as it is easily produced
by using quarter-wave plates in conjunction with polarizers.
Y -basis:
|ii = S|0i : right circular polarized : |i (9.9a)
|−ii = S|1i : left circular polarized : |i. (9.9b)
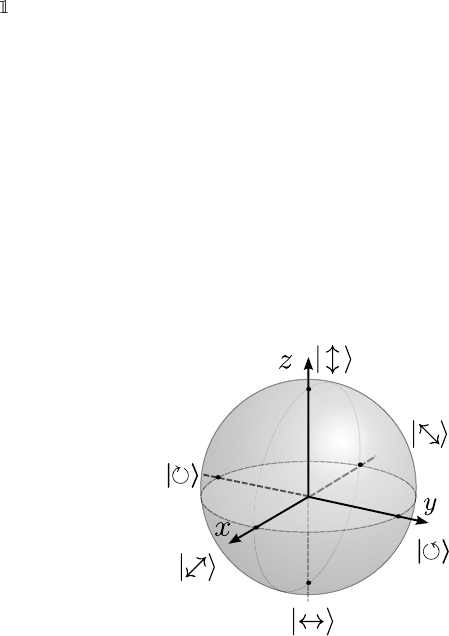
These states are indicated on the Bloch sphere in Figure 9.7.
FIGURE 9.7: Different photon polarization states indicated on the Bloch
sphere.
If a bit is encoded in a photon prepared randomly in one of the states of
Equations 9.7 and 9.8, can you find out which bit I have, without knowing my
preparation basis? The answer is, not with certainty. The best you can do is
to measure the photon in one of the 4 bases, chosen at random. What are the
chances that you pick the right one?
Say I prepared a |+i, which is the bit 1 encoded in the H basis. The
probability of your choosing the right basis for measuring is 1/2. If you chose
the wrong basis, then the probability of your measuring a 1 is 1/4. If I have a
whole string of n bits encoded in this fashion, the probability that you guess
right will be (1/4)
n
which becomes exponentially tinier as n increases!
Protocols for secure sharing of a random bit string between two parties
190 Introduction to Quantum Physics and Information Processing
rely on this property of encoding. We will review a few of them here to show
you how it works.
9.4.1 BB84 protocol
Due to C. Bennett and G. Brassard in 1984 [9], this protocol seeks to
generate a perfectly random bit string that is shared by Alice and Bob. The
beauty of the method is that the bit string does not exist until Bob measures
the qubits Alice has transmitted to him. Thus the security of the shared string
is guaranteed. The bits are randomly encoded either in the computational
basis ( ) or in the H basis. The steps followed are:
1. Alice produces a random bit string s
A
(for instance, by making quantum
measurements on an unpolarized stream of qubits) of length l.
2. She uses another random bit sequence m
A
to choose which polarization
state to encode each bit in: if (m
A
)
i
= 0 and the H basis if (m
A
)
i
= 1.
3. This encoded stream of photons is transmitted to Bob across a quantum
channel. We label the state of the i
th
photon by |φ
i
i.
4. Bob now uses a random bit string m
B
to choose a basis for measuring
each photon in this stream as it comes to him. He then has a string of
measurement outcomes s
B
.
5. After the measurements have been made, Alice announces her string m
A
over a public (insecure) channel.
6. Bob discusses with her and they discard those bits of s
A
and s
B
for
which the measuring bases do not match, i.e., those bit positions in
m
A
that do not match with m
B
.
7. The remaining bits, corresponding to the matching places, form a pos-
sible shared key. On an average, there will be half the original number
of bits in this set. a
The probability of Bob choosing the same basis as Alice is one half, so they
must start out with a string at least twice as long as the intended key. The
security of this method hinges on the inability to unambiguously distinguish
bits encoded in non-orthogonal bases.
Example 9.4.1. An example of the BB84 protocol is shown below, with the
shared key bits highlighted. Where the measurement bases are not the same,
the state measured by Bob is left blank, as it could randomly be |0i or |1i.
Information and Communication 191
Index 1 2 3 4 5 6 7 8 9 10 11 12 13 14
s
A
1 0 0 0 1 1 1 0 1 0 0 0 1 1
m
A
0 1 1 0 1 1 1 0 1 1 0 0 0 1
|φ
i
i ↔
l
l
l
l
l
l
l
l
↔ l l
l
l
m
B
0 0 0 1 1 0 1 0 1 0 0 0 1 1
s
B
1 0 1 0 1 1 1 0 1 1 0 0 1 1
Candidate key k = 11101001
What if there is an eavesdropper on the channel? Suppose Eve gains access
to the qubits in the quantum channel. She cannot copy the qubits and then
send them on their way to Bob, since the no-cloning theorem ensures she will
not have faithful copies. She can, however, measure the qubits in her own
choice of bases and then send them onward. In this situation, she has a 50%
chance of choosing the same basis as Alice. When Bob measures the qubits
again, he has a 50% chance of having chosen the same basis as Eve, so that
on the whole he has only a 25% chance of agreeing with Alice’s choice! But
how does he discover that the channel security has been compromised?
Alice and Bob decide to test this, by agreeing to compare a fraction of
their shared bit string. They can do this over a public channel, and if they
discover up to 25% mismatch then they know that the channel is suspect, and
they will not use it for their communication.
The protocol can be divided into three phases: first, the sending of the bit-
stream encoded in a quantum channel and the measurements made by Bob;
second, the public discussion of the data they obtain and third, the sifting,
testing and authentication of their data. We will discuss the last two a little
later.
9.4.2 BB92 protocol
The BB84 protocol was further refined in 1992 to use just two different
encoding states instead of four. The only two states Alice uses are |li and
|
l
i. This is sufficient, since they are not orthogonal and cannot be reliably
distinguished by the eavesdropped. The key steps are as follows:
1. Alice creates a random bit string s
A
,
2. She encodes a string 0’s in photons polarized randomly in the or H
basis according to the bits in s
A
.
3. Bob chooses a random string s
B
according to the bits in which he chooses
the basis or H to measure the photons. The measurement results form
a string m
B

Leave a Reply